Arthur Besse
cultural reviewer and dabbler in stylistic premonitions
- 62 Posts
- 145 Comments

 11·10 days ago
11·10 days agoThe tone which comes across in the video (linked from the other post I linked to in this post’s description) is unfortunately much less amicable than this article conveys.

 61·10 days ago
61·10 days agothe guy speaking off camera in the linked 3min 30s of the video is Ted Ts’o, according to this report about the session.
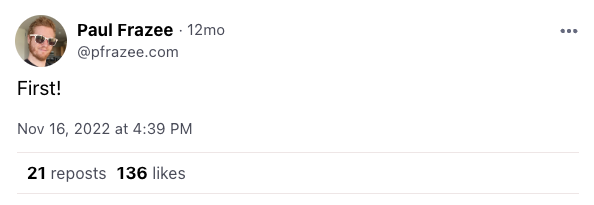
That label is there because I’m subscribed to XBlock Screenshot Labeller and it misclassified this image. (You can find here and here more info about how labelers in ATP work…)
i hope you’re joking but if you’re not i assume you live in the bay area? if you want to go to their pitch tonight, here’s its eventbrite.

 4·13 days ago
4·13 days ago
ip -br a(
-bris short for-briefand makesip’saddr,link, andneighcommands “Print only basic information in a tabular format for better readability.”)

 8·1 month ago
8·1 month agodemocracy dies in dark mode

 118·2 months ago
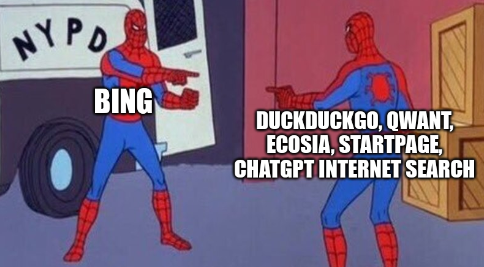
118·2 months agothis isn’t remotely how this meme is used lol


 19·2 months ago
19·2 months agowikipedia articles about him have been deleted twice:

 25·3 months ago
25·3 months ago/r/shittyaskredditwasn’t supposed to be an instruction manual 🙄

 2·4 months ago
2·4 months agoE: old thinkpad gang input: take the time to reapply thermal grease to the cpu at some point. It makes a huge difference.
What’s a “gang input”?
😂 it’s an input to this discussion from a member of the group of people (“gang”) who have experience with old thinkpads. and yes, if your old thinkpad (or other laptop) is overheating and crashing, reapplying the thermal paste is a good next step after cleaning the fans.

 31·4 months ago
31·4 months ago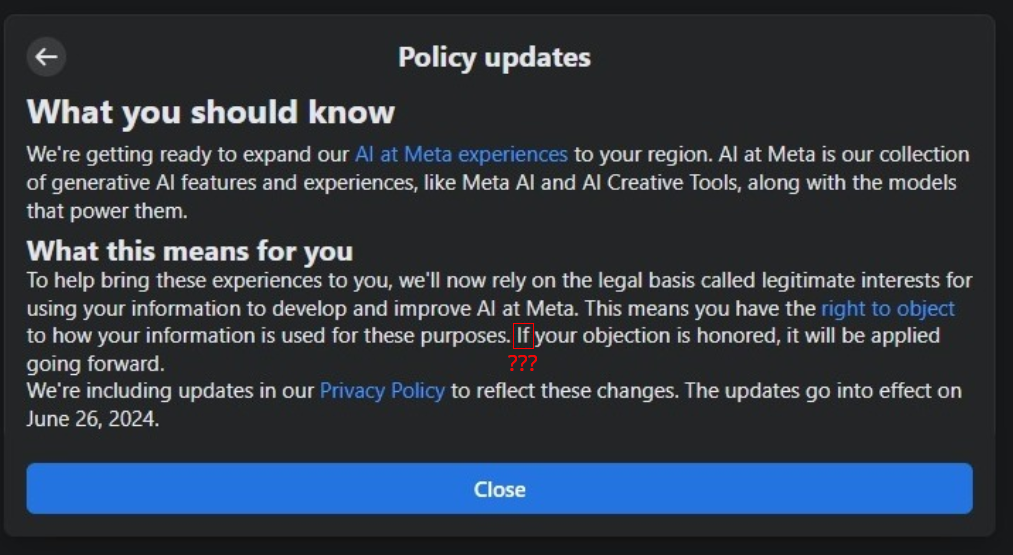
If your objection is honored, it will be applied going forward

 5·4 months ago
5·4 months agoxzbot from Anthony Weems enables to patch the corrupted liblzma to change the private key used to compare it to the signed ssh certificate, so adding this to your instructions might enable me to demonstrate sshing into the VM :)
Fun :)
Btw, instead of installing individual vulnerable debs as those kali instructions I linked to earlier suggest, you could also point debootstrap at the snapshot service so that you get a complete system with everything as it would’ve been in late March and then run that in a VM… or in a container. You can find various instructions for creating containers and VMs using debootstrap (eg, this one which tells you how to run a container with
systemd-nspawn; but you could also do it with podman or docker or lxc). When the instructions tell you to rundebootstrap, you just want to specify a snapshot URL likehttps://snapshot.debian.org/archive/debian/20240325T212344Z/in place of the usual Debian repository url (typicallyhttps://deb.debian.org/debian/).

 27·4 months ago
27·4 months agoA daily ISO of Debian
testingor Ubuntu 24.04 (noble) beta from prior to the first week of April would be easiest, but those aren’t archived anywhere that I know of. It didn’t make it in to any stable releases of any Debian-based distros.But even when you have a vulnerable system running sshd in a vulnerable configuration, you can’t fully demo the backdoor because it requires the attacker to authenticate with their private key (which has not been revealed).
But, if you just want to run it and observe the sshd slowness that caused the backdoor to be discovered, here are instructions for installing the vulnerable liblzma deb from snapshot.debian.org.

 2·4 months ago
2·4 months agobecause i thought the situation described by the post was tragicomic (as was somewhat expressed by the line from it quoted in the post title)









deleted by creator